Our Saskatoon IT Tips are from the Trusted professionals at Burnt Orange Solutions. We promise to have a one-hour response time for all your Saskatoon IT support needs. Honesty and respect are important to us. In our latest IT Expert tip Article, Gareth McKee, owner of Burnt Orange Solutions shares tips on protecting your business information.
The Basics of Protecting Your Business Information
Network Gateway Firewall
The first point of defense to protect your network from hackers and bots trying to gain access to your network. Ensure you speak with a professional IT company to ensure it is configured correctly.
Web protection
It is the easiest thing to click on a link not realizing it takes you to a very good fake website, this triggers the automatic download of a virus or ransomware. Web protection stops this happening by blocking known dangerous websites as well as legitimate websites which become infected.
Antimalware at server/workstation/tablets/cell phones
Everyone knows you should have anti-malware/virus on your PCs and Servers, but not everyone understands that you should have this software on all your devices. And don’t for 1 second think that Apple products are safe, they also need antimalware, as do your tablets and cell phones.
One more point on this, do not use free antimalware tools, they are free for a reason i.e. they are about as much use as a chocolate fire guard.
Anti-malware/spam at the email server
Specific email server antimalware and antispam software much be installed and configured correctly. This helps protect your staff from emails with dangerous links, virus payloads and generally makes them more efficient as their inbox will not be bombarded with 1,000s of annoying emails.
Secure WIFI
 WIFI must be secured using the latest encryption WPA2 and protected with a strong password or RADIUS security tools.
WIFI must be secured using the latest encryption WPA2 and protected with a strong password or RADIUS security tools.
Other tools which may be used to improve the security of WIFI networks include hiding the network, this way only computers which have been previously logged on to the network with be able to connect. You can also configure the WIFI network to only allow specific computers to connect.
One tactic which many businesses don’t do, but is a must, separate the WIFI networks, one for staff and one for guests. Only allow guests access to the internet and not on the business network, your laptops may be fully secured, but you don’t know the security standard of guests, they may very easily bring a virus in to your network.
Encryption
Consider full encryption of all your computers, in particular laptops. By design laptops are for travel, unfortunately, this allows the theft of them to be much easier than a server in a locked down building.
Encryption would ‘scramble’ all the data on the hard drive and the only way to decrypt the data is by having a user login and password. Even if the hard drive is removed from the laptop the data cannot be accessed.
Local and cloud image-based backups
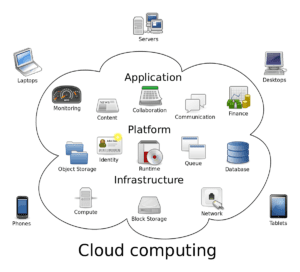 A good backup solution is like insurance, you never need it until you NEED IT.
A good backup solution is like insurance, you never need it until you NEED IT.
Don’t mess around with USB sticks which sit in a drawer. All businesses can afford and should use a business class backup service which provides:
- Image based backups – allows for quick recovery of whole systems
- Local backup – allows for quick recovery of files
- Cloud backup – allows for recovery of data even in the event of a total loss at the business location
- Encryption – stops hackers and thieves getting at your data.
User training
Staff members must be trained to use the software correctly, also to recognize dangerous phishing emails or other attempts at gaining access to your network.
Acceptable Use Policy
 Be sure to have an Acceptable Us Policy for your computers and networks. This plainly shows the staff members what they can and cannot do on the computers:
Be sure to have an Acceptable Us Policy for your computers and networks. This plainly shows the staff members what they can and cannot do on the computers:
- Are they allowed to use social media?
- Are they allowed to install software?
- Are they allowed to shop online?
Patch management
Patch management is a must for all devices on a network. New security holes are discovered every day on PCs, servers, switches, routers, firewall, WIFI access points, printers, scanners etc. all these devices can provide access to your network, ensure all patches and upgrades to all software and hardware are installed when they become available.
Proactive maintenance
We all know the value of maintaining our cars, yet very few people maintain their computers. From blowing out the insides of a computer to get rid of all the dust to hard drive checks which will save you hours if not days in the event of a hard drive failure.
The best solution here is to outsource the proactive testing and reporting to an IT support company, they will have the tools, the trained staff and the reporting to do this properly.
Firewall at server/workstation
Each device needs a firewall to improve its safe on the network. Often when a virus finds its way in to a network it will try to replicate itself across all the devices, a firewall on the PCs and servers helps prevent this.
File and folder security permissions
To prevent leakage of information from your business it is paramount that security rules are in place to prevent a staff member from gaining access to information they should not have. Whether malicious or not, this can cause at best an HR headache at worst business secrets could find their way to your competitors.
Users should not have administration rights
Staff members should not have administration rights to their local computer, it helps prevent the installation of unknown software and the spreading of viruses.
Passwords
We now speak about passPHRASES rather than passwords as you can have spaces in the string of characters. A good passphrase should have at least 14 characters and be changed at a minimum quarterly.
Do not allow the use of Dropbox etc.
Unless authorized by the management of a company, Dropbox and the like should not be allowed. A helpful staff member today who uses Dropbox to work at home may leave the company next week and have a lot of business information on their home computer.
Also, Dropbox can aid the spread of viruses and ransomware.
On a side note, do not use Dropbox as a backup solution, if a file on your PC becomes corrupt, the copy in Dropbox will also become corrupt. It is not designed as a backup solution.